Products
Solutions
Resources

The Center for Internet Security (CIS) benchmarks are a set of compliance best practices for a range of IT systems and products. These benchmarks provide the baseline configurations to ensure both CIS compliance and compliance with industry-agreed cybersecurity standards.
CIS compliance matters because cybersecurity vulnerabilities emerge whenever IT systems aren't configured correctly. The financial stakes for getting this right have never been higher: According to IBM's 2025 Cost of a Data Breach Report, U.S. organizations are experiencing an all-time high average data breach cost of $10.22 million in 2025 — a 9% year-over-year increase that significantly exceeds the global average.
Organizations face pressure from regulators, board members and customers to demonstrate effective cyber risk management. CIS benchmarks offer practical, community-vetted guidance for securing everything from cloud infrastructure to operating systems.
This article explores everything you need to know about CIS compliance and benchmarks, including:

The Center for Internet Security (CIS) is a nonprofit organization that develops cybersecurity best practices through collaboration with security experts worldwide. The organization brings together professionals from private companies, government agencies and research institutions to identify and promote effective security standards. The aim is to take a collaborative approach to improving cybersecurity and responding to known cyber threats.
To achieve this, CIS provides tools and resources to help organizations improve IT governance and respond to cyber threats. Many of these resources are freely available. The organization actively monitors threats through the Multi-State Information Sharing and Analysis Center (MS-ISAC), which supports national and local governments with cybersecurity notifications, threat reports and governance resources.
CIS compliance means meeting CIS security standards. CIS-compliant organizations will have an established baseline for protecting their systems and data from cyberattacks. This baseline should meet the CIS benchmarks, which cover a wide range of vendors and systems.
Though CIS benchmarks stand alone, compliance with them is part and parcel of a broader IT risk management strategy. CIS benchmarks align with essential industry regulations, including the NIST Cybersecurity Framework, ISO/IEC 27001:2022, PCI DSS 4.0, CMMC, GDPR and HIPAA. As a result, organizations that prioritize CIS compliance will also achieve compliance with other industry regulations.
For public companies, regulatory pressure has intensified. The SEC's cybersecurity disclosure rules require reporting material incidents within four business days of determining materiality, while annual disclosures must cover risk management strategies and governance structures. These requirements connect directly to CIS Control 17 (Incident Response Management) and demand governance frameworks that boards can oversee effectively.
Compliance scores measure how well an organization adheres to CIS benchmarks across its systems. These scores reveal where security improvements are needed and help internal audit teams prioritize their reviews. Rather than manually checking every system configuration, audit teams can use compliance scores to identify areas requiring immediate attention.
"As global risks increase, we will continue to see the CISO role be elevated within organizations," says Charlie Lewis, Partner at McKinsey. This elevation brings increased scrutiny of cybersecurity frameworks like CIS benchmarks.
CIS benchmarks are frameworks for calibrating a range of IT services and products to ensure the highest standards of cybersecurity and are a vital part of your organization's CIS compliance objectives. They're developed through a collaborative process with input from experts within the cybersecurity community.
There are more than 100 different benchmarks covering a range of well-known vendors and systems. CIS benchmarks provide compliance guidance across all areas of an IT network, including operating systems, servers, office software and network devices.
CIS benchmarks are free to download and use. Each benchmark document covers everything from initial setup to detailed configuration recommendations for specific IT systems. The guidance undergoes quarterly updates to reflect new software iterations and emerging security threats. CIS benchmarks represent the baseline settings needed to secure IT systems against known vulnerabilities.
Organizations worldwide — from healthcare providers to financial institutions — use these benchmarks to enhance their cybersecurity posture. The frameworks integrate with existing IT risk management policies and internal audit procedures. Internal audit teams use CIS benchmarks to evaluate system configurations, then implement recommended CIS controls to strengthen defenses against cyberattacks.
The CIS Benchmarks August 2025 Update introduced significant changes, including CIS Microsoft Windows Server 2019 STIG Benchmark v4.0.0, CIS AWS End User Compute Services Benchmark v1.2.0 and CIS Docker Benchmark v1.8.0, reflecting the evolving security requirements for cloud and container environments.
Each benchmark follows a consistent structure. The opening section provides an overview, definitions and identifies the intended audience.
The main content consists of detailed recommendations for configuring specific IT systems. A single CIS benchmark may contain hundreds of recommendations, organized by policy area and system component.
Every recommendation includes:
Recommendations are classified as either "scored" or "not scored." Scored recommendations are mandatory for achieving CIS compliance. Failing to meet these recommendations lowers the overall benchmark score. Not scored recommendations provide additional security guidance but don't affect compliance scoring.
Each benchmark includes a checklist appendix that helps teams track compliance progress for every recommendation.
CIS benchmarks emerge from a rigorous, community-driven development process involving cybersecurity experts from around the world.
The process begins with a panel of security professionals who create, discuss and test draft benchmark recommendations. Once the panel reaches consensus on the draft guidance, it's published for broader community review.
During the second phase, cybersecurity professionals globally review the proposed benchmark. The expert panel collects feedback, evaluates suggested changes and refines recommendations to reflect best practices. This consensus-based approach ensures benchmarks represent tested, practical security guidance.
CIS updates benchmarks when vendors release new versions of IT systems or when emerging threats require revised security configurations. Recent major updates include benchmarks for Windows Server 2025, Docker Server v28, AWS End User Compute services, Apple macOS 14 and 15, Cisco NX OS and DigitalOcean cloud infrastructure.
Some legacy benchmarks — including those for Zoom, Check Point and Juniper — are scheduled for retirement unless renewed community support emerges.
To help organizations with implementation, each recommendation within a CIS benchmark is assigned a level-1 or level-2 profile. The profile levels represent the potential impact of a recommendation on the organization's IT systems and cybersecurity defense.
It helps organizations understand which recommendations meet their cybersecurity needs and available resources. Profiles reiterate the importance of using a test environment when implementing CIS benchmark recommendations.
Organizations should implement level-1 recommendations first to establish security baselines, then evaluate level-2 recommendations based on their specific risk tolerance and operational requirements.
Both profile levels emphasize testing configurations in non-production environments before deploying to production systems.
CIS benchmarks help organizations configure IT systems using frameworks developed by leading cybersecurity experts. These guidelines address cybersecurity vulnerabilities that emerge when systems aren't configured correctly.
Every component in an organization's IT network — from operating systems to cloud services — can create security gaps if misconfigured. CIS benchmark compliance provides tested frameworks for securing these systems while building a foundation for meeting other regulatory requirements.
Benefits of CIS compliance include:
"It's difficult for even the most seasoned practitioners of cyber to understand it all, so it's going to be hard for the board to understand it," says Derek Vadala of Bitsight Technologies. This reality makes standardized frameworks like CIS benchmarks valuable for communicating security posture to non-technical stakeholders.
CIS benchmarks provide configuration standards for the full range of IT technologies and systems that enterprises depend on. Organizations can use these standards to strengthen specific areas of their IT infrastructure.
CIS benchmarks guide the proper configuration of different server software from various vendors. This includes commonly used server software such as VMware or Microsoft Windows Server. The aim is to strengthen cybersecurity through best practice configurations across different areas of the IT server system.
There are CIS benchmarks for database servers, web servers, DNS servers and authentication servers. Recommendations cover storage settings and restrictions, admin controls and server settings.
Print devices have become targets for cyber threats as entry points into organizational networks. Benchmarks cover file sharing protocols, server configurations and secure wireless network access to protect these often-overlooked endpoints.
As organizations migrate infrastructure to cloud platforms, configuration security becomes critical. CIS provides benchmarks for Amazon Web Services, Microsoft Azure, Oracle Cloud Infrastructure and Google Cloud Platform. Recent additions include DigitalOcean cloud infrastructure and AWS End User Compute services.
Recommendations cover network security settings, identity and access management, compliance controls and governance frameworks specific to cloud environments. These benchmarks help organizations maintain security standards as they adopt multi-cloud strategies.
CIS benchmarks address mobile operating systems from Apple (iOS and iPadOS) and Google (Android). As mobile devices access enterprise data and applications, securing these endpoints protects against data breaches. Recommendations cover browser settings, developer options, app permissions, privacy controls and operating system configurations.
CIS benchmarks provide configuration guidance for desktop applications commonly used in enterprises, including Microsoft Office and major web browsers (Google Chrome, Mozilla Firefox, Safari, Microsoft Edge).
These recommendations help organizations secure the productivity tools employees use daily. Guidance covers browser security settings, management of third-party add-ons, server connections and device management policies.
Network infrastructure forms the backbone of enterprise IT systems. CIS benchmarks help configure network devices and hardware from vendors, including Cisco, Juniper, Check Point Firewall and Palo Alto Networks.
Securing network devices strengthens the entire IT governance strategy by closing vulnerabilities at the infrastructure level.
Operating systems run enterprise workstations and servers, making their security configuration fundamental to overall cybersecurity. CIS provides benchmarks for Linux distributions, Microsoft Windows (desktop and server versions) and Apple macOS. Current benchmarks include Windows Server 2025 and macOS 14 and 15.
Recommendations cover driver installation protocols, user profile management, remote access restrictions and system hardening procedures that reduce attack surfaces.
As enterprises adopt containerized deployments and modern development practices, new benchmarks address these technologies. Recent additions include Docker Server v28 and Kubernetes configurations.
These benchmarks help organizations secure DevOps pipelines and container orchestration platforms that power contemporary application architectures.
CIS certification verifies that cybersecurity products can be configured to meet CIS benchmark recommendations. This certification helps customers identify products that align with industry-standard security configurations, making it easier to achieve and maintain CIS compliance.
To pursue certification, organizations must first join the CIS Security Software Vendor (SSV) program. The certification process requires testing products against specific benchmark recommendations and documenting compliance evidence. CIS validates the test results before issuing certification, after which organizations can display the CIS certification mark alongside their products.
Organizations seeking CIS certification must be members of the CIS Security Software Vendor group before submitting applications. Certification applies to one specific CIS benchmark.
The certification process requires comprehensive testing against each recommendation in the chosen benchmark. Organizations submit detailed documentation showing pass/fail status for every recommendation, including explanations for any failures and any mitigating factors.
CIS typically reviews certification applications within two weeks, though the timeline extends when applications are incomplete or when organizations need to address compliance gaps. The process now requires continuous attestation rather than one-time certification, reflecting the reality of rapid configuration changes in modern IT environments, particularly for cloud-based services.
Security teams face a fundamental challenge with CIS compliance: manual verification doesn't scale across enterprise infrastructure. CISOs managing thousands of servers, cloud instances and network devices can't rely on quarterly audits to identify misconfigurations that create exploitable vulnerabilities. By the time traditional compliance reviews detect gaps, systems may have operated outside benchmark recommendations for months.
Leading governance solutions like Diligent solve this by continuously analyzing configurations across entire IT estates, identifying deviations from CIS benchmarks in real time and prioritizing remediation based on actual risk rather than just compliance scores.
Diligent IT Risk Management centralizes CIS benchmarks alongside NIST, ISO 27001, PCI DSS and GDPR frameworks in a single platform. Rather than managing separate compliance programs, security teams work from unified control libraries where a single configuration improvement advances multiple regulatory requirements simultaneously.
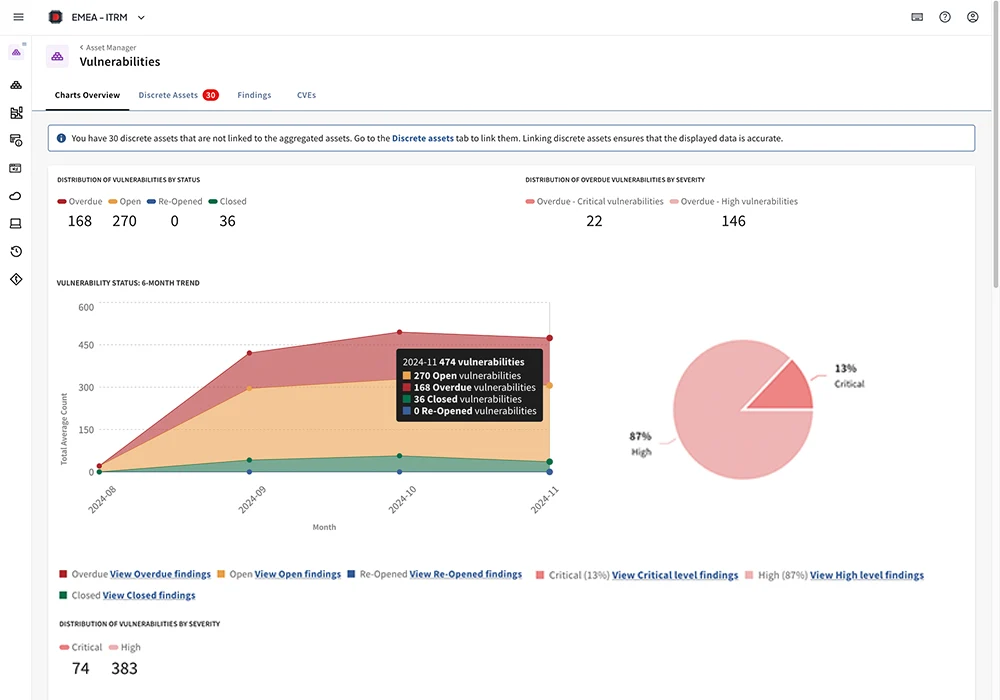
The platform automates mapping between frameworks, showing how CIS benchmark implementation satisfies corresponding controls in other standards. This approach maximizes the value of compliance investments while reducing redundant verification work.
Diligent's AI-powered cyber risk management capabilities extend this unified approach to vulnerability management by centralizing data from third-party security tools into a single cyber risk hub. This integration provides CISOs and boards with comprehensive visibility across the entire cyber risk landscape, enabling faster, data-driven decisions through asset-to-vulnerability mapping and business-impact prioritization.
Continuous scoring provides real-time visibility into compliance posture across all frameworks, helping CISOs prioritize remediation efforts based on risk exposure rather than audit schedules.
Organizations operating globally face CIS compliance complexity multiplied across subsidiaries, regional offices and legal entities subject to varying regulatory requirements. Diligent Entities brings AI-driven analysis to regulatory and entity data management, tracking compliance obligations across organizational structures while maintaining visibility into which CIS benchmarks apply to specific jurisdictions.
The platform connects entity-level compliance data with broader IT risk management, ensuring that configuration standards account for regional variations in cybersecurity regulations. This centralized approach prevents compliance gaps that emerge when subsidiary IT teams operate independently without coordinated oversight.
"Tell the board what they need to know, not what you know," says David Platt of Moody's. Technical CIS compliance data means little to board members who need to understand business risk, not benchmark scores.
Diligent Boards translates technical compliance findings into governance-focused reporting that audit and risk committees can actually use for oversight. The platform synthesizes CIS compliance status, vulnerability trends and remediation progress into professional board materials that communicate cybersecurity posture clearly.
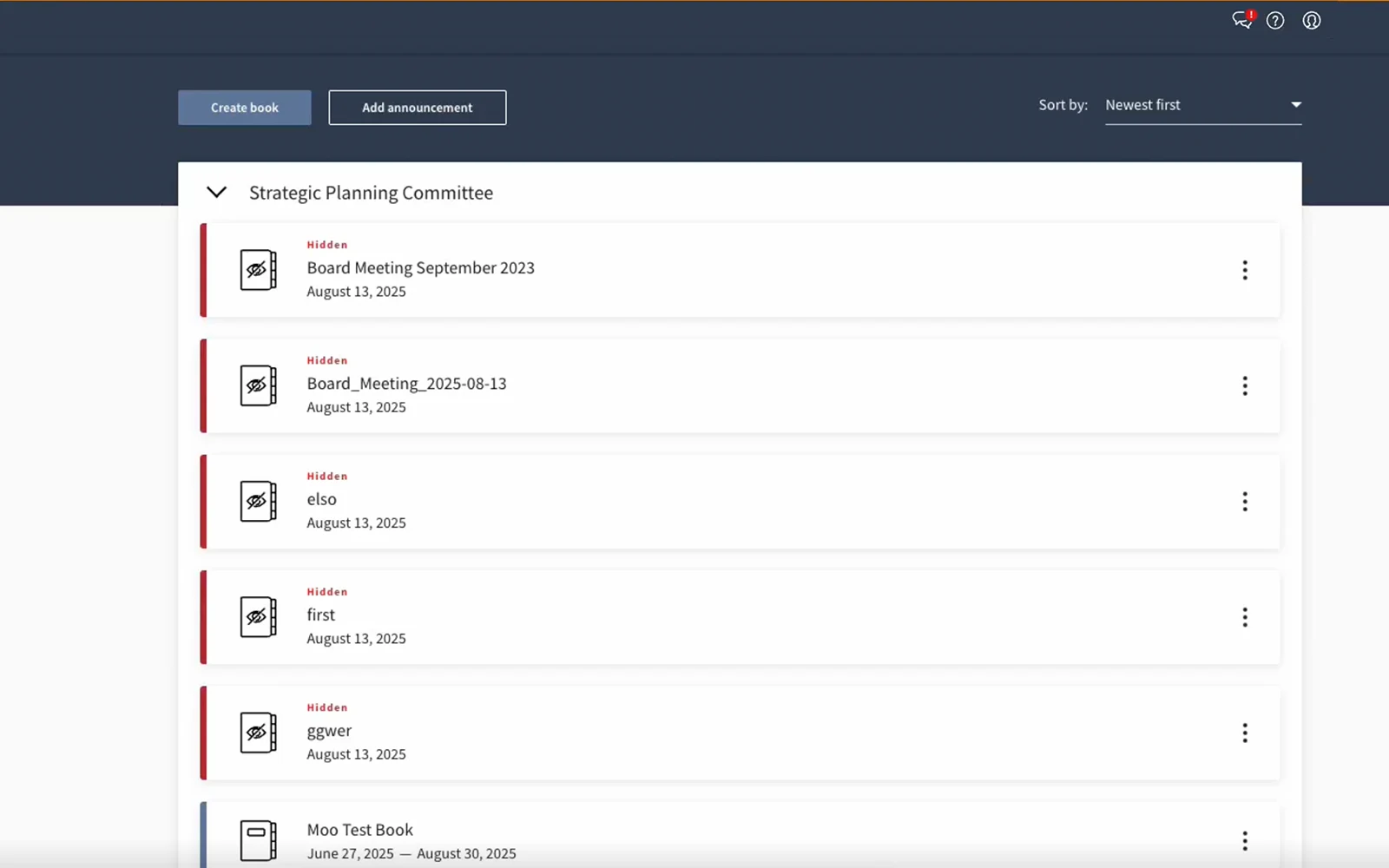
Security teams can demonstrate how CIS compliance programs address SEC disclosure requirements, satisfy regulatory frameworks and mitigate specific business risks. Multi-lingual support and template-driven workflows ensure consistent reporting across global operations while maintaining the security and audit trails that regulatory environments demand.
By handling the repetitive work of compliance verification, AI-powered platforms free security professionals to focus on the strategic analysis, threat hunting and architecture decisions that actually improve organizational security posture.
Ready to transform your approach to CIS compliance with automated risk management and board-ready governance reporting? Request a demo to see how Diligent's integrated platform turns benchmark implementation into strategic risk intelligence.
CIS controls provide high-level security practices and principles, while CIS benchmarks offer detailed, system-specific configuration guidance for implementing those controls. Think of CIS controls as the "what" and CIS benchmarks as the "how" of cybersecurity implementation.
Most enterprise organizations start with Level 1 profiles for broad coverage, then implement Level 2 profiles for critical systems. Level 1 provides essential security with minimal operational impact, while Level 2 offers enhanced security for high-risk environments but may require additional testing and resources.
CIS benchmarks integrate well with NIST Cybersecurity Framework 2.0, HIPAA and other major standards. The official NIST CSF 2.0 mapping allows organizations to achieve multiple compliance objectives simultaneously through unified CIS implementation.
The most effective tools provide continuous monitoring, automated configuration management and integrated reporting across multiple compliance frameworks. Solutions that offer real-time scanning, effective prioritization using analytics and unified detection capabilities deliver the greatest operational efficiency and risk reduction.
Schedule a demo to discover how Diligent streamlines compliance while providing the visibility executives and boards need to make informed cybersecurity decisions.