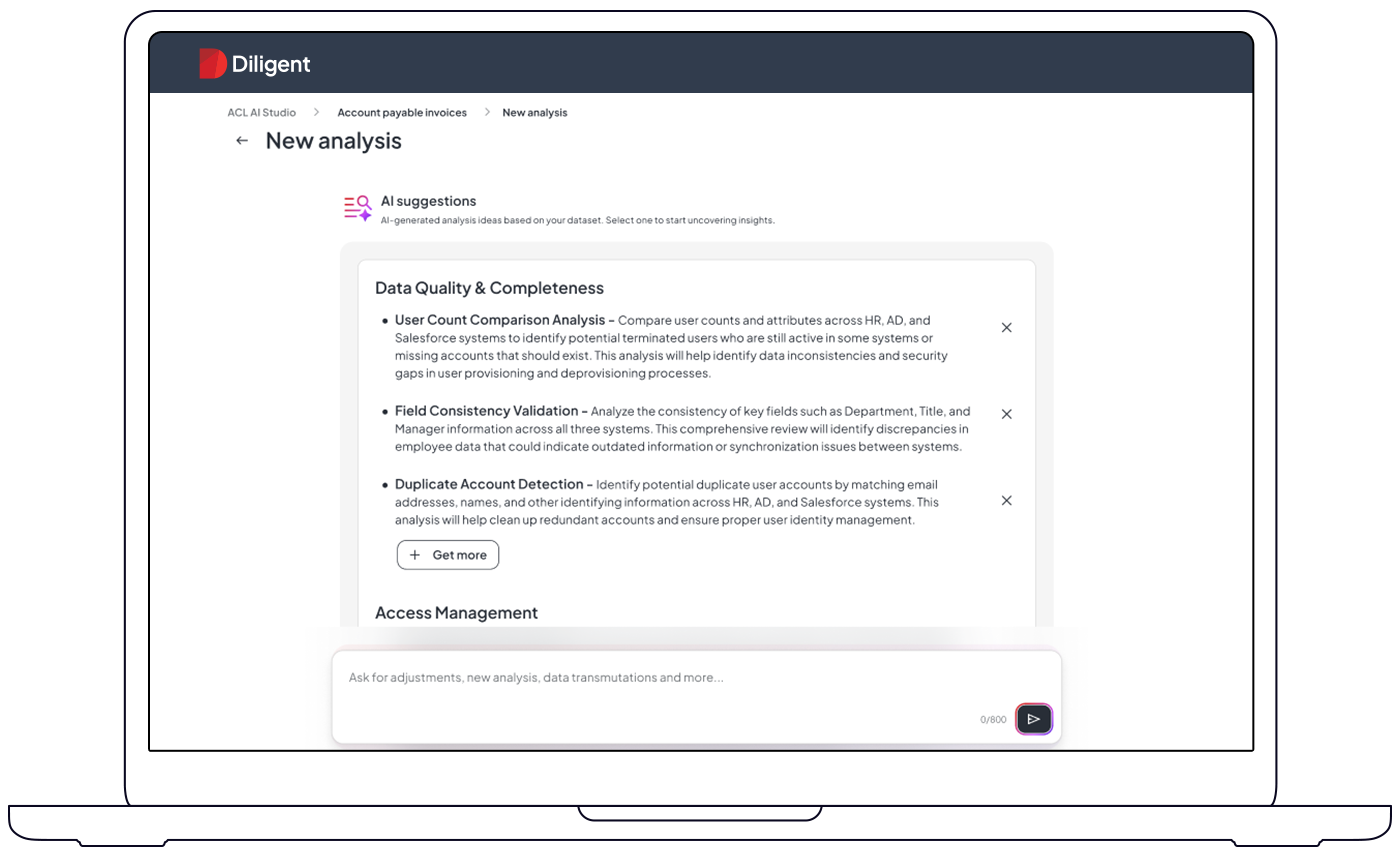
Uncover audit & risk insights instantly with a natural language interface
Unleash instant, AI-powered insights — just ask. ACL Analytics lets any audit or risk pro probe 100% of your data, automate monitoring, and flag issues before they escalate. No code. No barriers. No black box — every result is transparent and audit-ready.
AI-powered, script-compatible analytics in three simple steps
Get more from your data, quickly and easily
Natural language analytics
Run complex audits with simple prompts. Anyone on your team can uncover insights—no coding required.
Full ACL script compatibility
Transparent logging & traceability
Automation robots for continuous assurance
More to love
Ready to detect risk before it escalates?
Experience a smarter way to analyze, monitor, and act on your data. Start your free trial and see how ACL Analytics transforms assurance.
Trusted by thousands of audit and risk teams globally
Frequently Asked Questions
Your question not answered here? Reach out to talk with us.
What is ACL Analytics?
A powerful analytics engine that lets audit, risk, and compliance teams analyze and test large datasets.
What is Continuous Monitoring?
Can ACL integrate with my ERP or HR system?
Does it require technical skills or coding knowledge?
Is my data secure and compliant?
How is this different from other GenAI or BI tools?
Experience AI-driven ACL Analytics — No code, no delay
Ready to uncover risk faster, simplify audits, and boost team productivity? Get hands-on with AI analytics built for today’s audit and risk teams — and see what smarter oversight really looks like.
Take a guided tour