Products
Solutions
Resources

When a cyberattack hits, boards need immediate answers: What happened? What's at risk? Are we compliant with SEC disclosure requirements? Too often, cybersecurity teams and governance, risk and compliance (GRC) departments arrive with different data, conflicting timelines and no unified risk assessment.
GRC cybersecurity integration solves this problem by connecting technical security operations with governance frameworks, risk processes and compliance requirements. Instead of parallel functions that converge only during crises, integrated approaches ensure cyber teams and GRC departments share data, coordinate assessments and deliver consistent intelligence to boards.
The challenge isn't theoretical. Directors rate current business risk at 6.8 out of 10 according to the Director Confidence Index from Diligent Institute and Corporate Board Member, with cyber threats consistently ranking among their top concerns.
Meanwhile, SEC cybersecurity disclosure rules require public companies to report material incidents within four business days — a timeline that assumes cyber and GRC teams already work in coordination. Organizations still operating with siloed functions face regulatory exposure, slower threat response and incomplete board reporting.
To this end, this article covers the following:
GRC in cybersecurity involves establishing frameworks of policies, procedures and controls to ensure that cybersecurity objectives align with business goals while meeting regulatory requirements. The three dimensions of GRC empower organizations to:
Integrating cybersecurity with your GRC program allows companies to take a comprehensive approach to risk management from both policy and digital risk standpoints.
Rather than operating in separate spheres where cyber teams focus on threat monitoring while GRC departments manage organizational compliance, effective integration creates shared visibility, coordinated response capabilities and unified board reporting.
The relationship between GRC and cybersecurity has evolved from parallel functions to interdependent capabilities. GRC provides the governance structure, risk frameworks and compliance processes that guide cybersecurity strategy.
On the other hand, cybersecurity delivers the technical controls, threat intelligence and incident response capabilities that implement GRC requirements.
This interdependence manifests in multiple ways:
Organizations that recognize this relationship can build integrated programs where cyber and GRC teams collaborate on risk identification, share data for comprehensive assessments and deliver unified reporting to boards and regulators.
The urgency around GRC cybersecurity integration stems from three converging forces: the technical complexity of modern cyber threats, the expanding regulatory landscape and the board-level governance expectations that now accompany cyber risk oversight.
Distributed work environments, cloud infrastructure and digital business models have fundamentally changed how organizations secure their operations. Attack surfaces now span multiple cloud providers, remote endpoints, third-party integrations and legacy systems, creating interconnected risk that no single team can manage in isolation.
Vulnerability scanners may identify hundreds of potential issues, but GRC teams determine which ones actually threaten business operations or regulatory compliance.
Conversely, compliance requirements mean nothing without cybersecurity teams to implement the actual protections. This interdependence means siloed approaches leave gaps that attackers exploit.
The regulatory landscape has evolved from isolated compliance requirements into an interconnected web of obligations. Organizations navigate state privacy laws like:
Organizations attempting to manage these obligations through separate teams create duplicate efforts, inconsistent reporting and compliance gaps that regulators increasingly scrutinize during audits.
Nation-state actors, cybercriminal organizations and hacktivists exploit global tensions to target critical infrastructure and enterprises. These threats require governance frameworks that connect technical security measures with business continuity planning, regulatory reporting and board oversight.
Organizations can no longer treat cyber risk as solely a technical problem. When geopolitical events create cyber threats that could disrupt operations, boards need integrated intelligence that shows technical risk, business impact and governance implications simultaneously.
Cyber risk represents such a significant business threat that cybersecurity and technology teams help establish the tone for enterprise risk posture. Organizations achieve better outcomes when they integrate GRC functions with cybersecurity operations rather than treating them as separate domains.
"Compliance drives change. But it doesn't make you more secure," says Myrna Soto, Founder and CEO of Apogee Executive Advisors and former CISO at Comcast.
This insight captures why integration matters: compliance without security leaves organizations vulnerable while security without governance frameworks lacks accountability and board oversight.
Integration delivers outcomes that siloed approaches cannot provide.
Integration enables better risk identification and response. When cyber teams identify vulnerabilities, GRC frameworks determine business impact, compliance implications and board reporting requirements.
When GRC teams assess controls, cyber operations provide technical validation and remediation capabilities. This collaboration creates more accurate risk assessments and faster responses to emerging threats.
The foundation of successful integration is trust between functions. Cyber teams must trust that GRC assessments reflect actual business risk rather than checkbox compliance. And GRC teams must trust that cyber operations provide complete visibility into the threat landscape.
Organizations can take concrete steps to build effective partnerships between cybersecurity and GRC functions. Success requires addressing culture, communication, technology and organizational structure.
Collaboration starts with culture. Organizations need corporate cultures that encourage working together to reach common goals rather than finger-pointing, being overly technical or simply checking compliance boxes. Cultures of fear or shaming alienate the partners teams should build relationships with to facilitate objectives.
Establishing trust between cyber and GRC teams takes time but provides the foundation for integration. This means understanding what each function tries to achieve and working toward common goals.
It requires recognizing that cyber teams and GRC departments bring complementary expertise that strengthens risk management when combined.
"Shared accountability will lead to the most conducive partnership, and this can come with shared goals and shared objectives," says Myrna Soto, Founder and CEO of Apogee Executive Advisors.
Different teams often use different terminology to describe similar concepts. Security teams discuss "vulnerabilities" while compliance teams reference "control gaps" and risk managers identify "exposures." This language gap creates confusion and impedes collaboration.
Organizations should:
This shared language enables clearer communication and better integration of cyber risk into enterprise risk management.
When distilling GRC cybersecurity frameworks, metrics, evaluations and reviews for boards, focus on what matters to business outcomes. John Zangardi, former CEO of Redhorse Corporation, calls this the "so what" effect. What's the probability of a risk occurring? What are the consequences? What does it mean to operations and profitability?
"Putting it into business terms works magic in the organization. When I would brief the Homeland Security Secretary I'd say, 'Look, if this particular system goes down, that stops all transit on the St. Lawrence Seaway.' They get that, that makes the news," says Zangardi.
When contextualizing cyber risk, communicate with line leaders or technology leaders about specific impacts.
Use data to resolve differing views and gain executive and board support for strategic priorities. This helps stakeholders understand what needs to be done from a business context rather than getting lost in technical details.
Since compliance and GRC typically fall under audit committee purview, bringing cybersecurity into that oversight creates better understanding of IT risks. Organizations increasingly treat cybersecurity frameworks, artifacts and controls similarly to how they approach SOX and financial reporting controls.
"We absolutely cover cyber in audit," says Myrna Soto regarding organizations she works with. They examine everything from cybersecurity frameworks to control artifacts using approaches similar to financial control audits. This helps audit teams share and better understand risks since IT systems underpin virtually every business operation.
While audit teams must maintain independence, partnership models enable better evaluation of mitigation controls and remediation plans. This moves organizations beyond check-the-box approaches toward integrated assurance that provides boards comprehensive risk visibility.
Boards need clear, actionable cyber risk information presented in governance context. This requires establishing reporting protocols that translate technical cyber metrics into board-level intelligence about business risks, regulatory compliance and strategic implications.
"A heatmap is a communication tool," says Inna Barmash, Chief Legal Officer and Corporate Secretary at Amplify. Visual communication tools help boards quickly grasp risk landscapes and priority areas requiring attention.
Technology selection represents a critical decision point for GRC cybersecurity integration. The right technology enables collaboration between cyber and GRC teams by facilitating information gathering, cross-team data sharing and presenting unified views to boards.
"By far our most commonly used feature is search. Having that single source of truth can help break down silos," says Curtis Duncan, Senior Manager of Customer Success at Diligent.
Organizations should evaluate integrated risk management platforms based on:
Technology platforms that bring cyber and GRC together create several advantages. Unified platforms minimize manual data entry, reducing potential for human error. They consolidate previously scattered information into single sources of truth and provide boards with clear, comprehensive management information visualizing cyber risk in business context.
For enterprise organizations managing comprehensive cyber risk across global operations, integrated technology platforms address the siloed information and fragmented reporting that traditional point solutions create.
The Diligent One Platform unifies board management and GRC activities in a single interface that eliminates the need for multiple disconnected vendors. The platform integrates with 100+ third-party systems, including Salesforce, SAP, Microsoft, Oracle and S&P Global to create consolidated views of risk across organizations.
Board-ready reporting templates for cyber risk, audit, investor engagement and ERM enable consistent communication to directors.
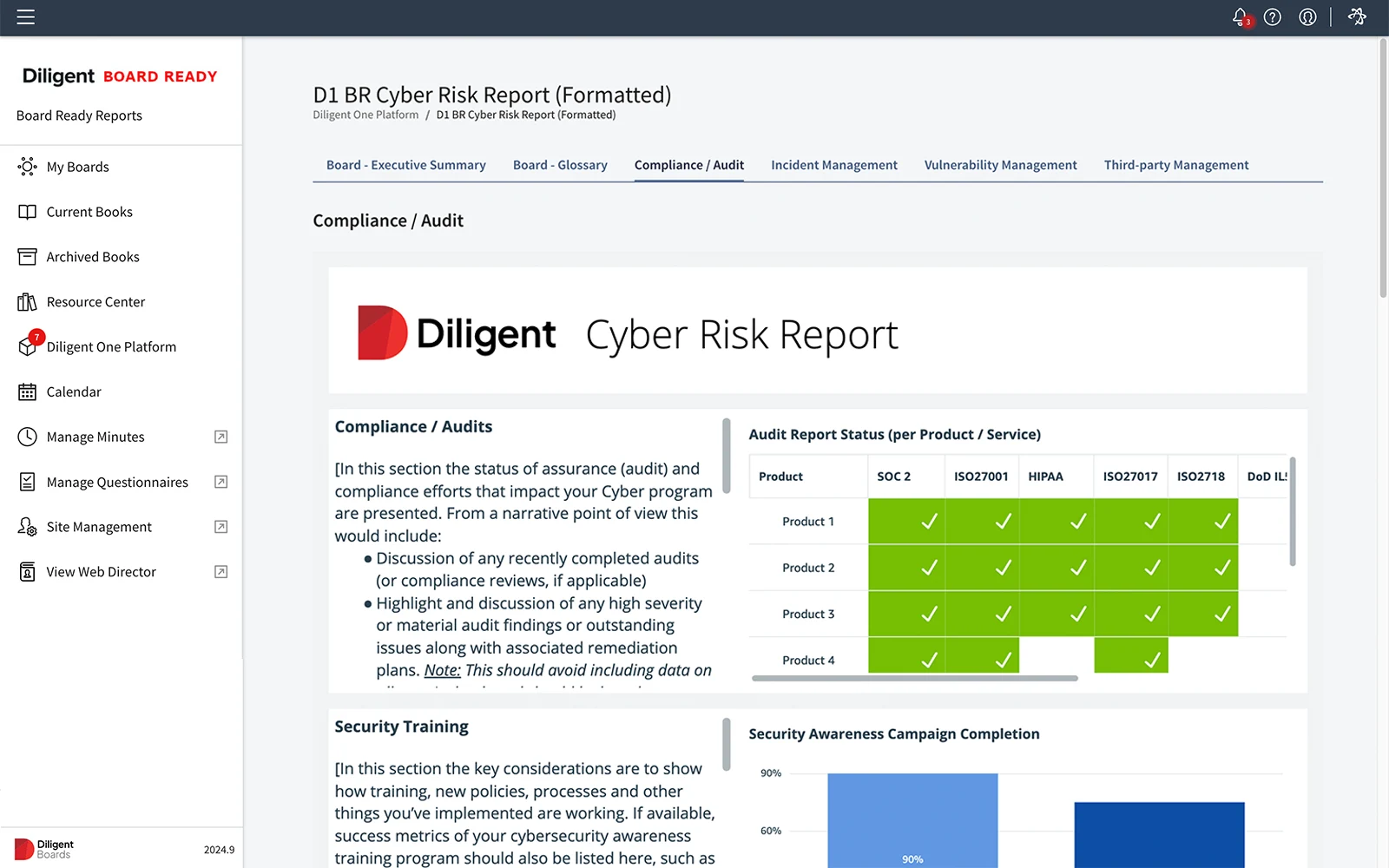
Configuration-over-customization approaches implement prescriptive, proven practices without requiring extensive custom development. Advanced analytics and data automation capabilities surface insights from integrated data.
Diligent IT Risk Management provides the first-ever cyber GRC hub using AI to centralize all vulnerabilities into a single view of cyber risk. Winner of Datos Insights' 2025 Cyber Impact Award for Best AI-enabled Capability for Board-level Cyber GRC, the platform delivers comprehensive cyber risk orchestration capabilities.
To provide effective vulnerability management, the centralized cyber risk hub unifies IT and cyber risk data across departments, systems and third parties into consolidated views.
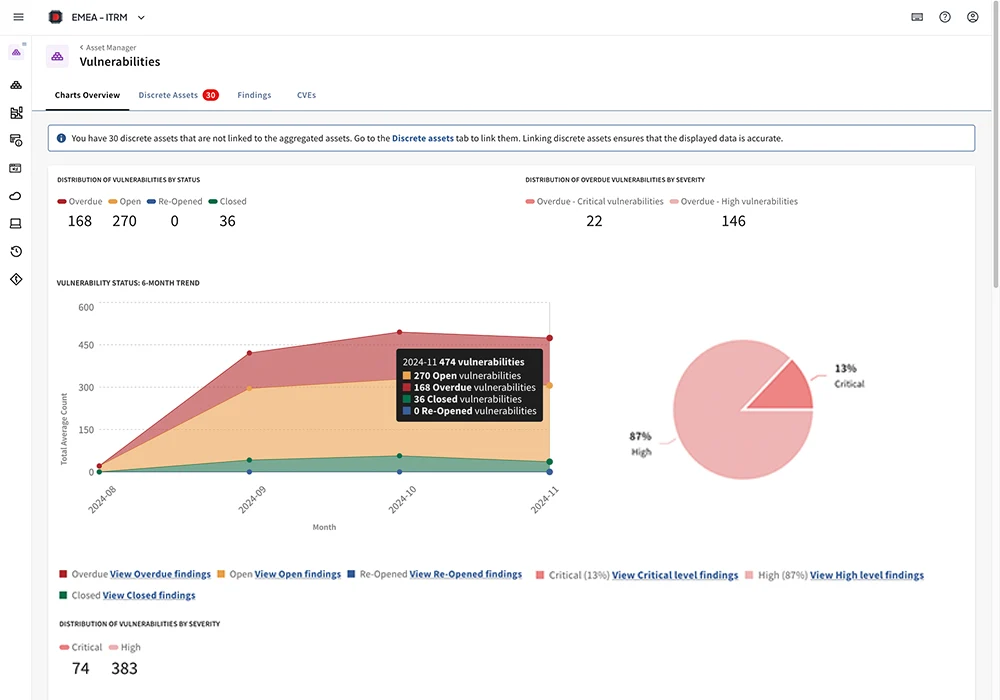
Integration with leading vulnerability scanners aggregates findings from multiple security tools, while asset-to-vulnerability mapping prioritizes remediation based on business impact rather than technical severity alone.
For organizations requiring comprehensive risk orchestration beyond cyber, Diligent ERM integrates cybersecurity risk into enterprise-wide risk management. AI-powered risk identification benchmarks against 180,000+ real-world risks from SEC 10-K reports.
Moody's risk benchmarking data provides external risk intelligence and credit sentiment scores that contextualize internal assessments. The platform creates single sources of truth for strategic and operational risk while delivering risk-informed board reporting through executive dashboards and customizable templates.
Technology platforms provide the foundation for GRC cybersecurity integration, but successful implementation requires more than software deployment. Organizations must address culture, establish shared processes and maintain executive commitment to integration over time.
Ready to see how integrated GRC cybersecurity platforms deliver comprehensive cyber risk intelligence to your board? Book a demo to see Diligent in action.
Traditional cybersecurity programs focus primarily on technical controls, threat detection and incident response.
On the other hand, cybersecurity GRC adds governance structures, risk management frameworks and compliance processes that connect cyber activities to business objectives and board oversight.
AI transforms GRC cybersecurity platforms by automating risk identification, aggregating vulnerability data from multiple sources, providing intelligent risk scoring based on business context and delivering real-time analytics.
The SEC's cybersecurity disclosure rules require boards to demonstrate oversight of cybersecurity risk management.
This includes understanding the organization's cyber risk strategy, overseeing management's implementation of security controls, receiving regular cyber risk reporting and disclosing material cybersecurity incidents within four business days.
Organizations can assess GRC cybersecurity integration maturity by evaluating several factors:
Ready to transform cyber risk oversight with integrated GRC capabilities? Schedule a demo to see how Diligent's platform delivers comprehensive cyber risk intelligence to boards.