Smarter screening. Faster compliance.
70%
Reduce adverse media review time by over 70% with AI-powered summaries.
19m+
Screen against 19m entities using our exclusive ownership & affiliation network data.
190+
Combine human expertise and AI to power investigations worldwide in more than 190 countries.
1
Replace multiple vendors with one single platform of integrated data and services.
Comprehensive third-party risk management across the entire lifecycle
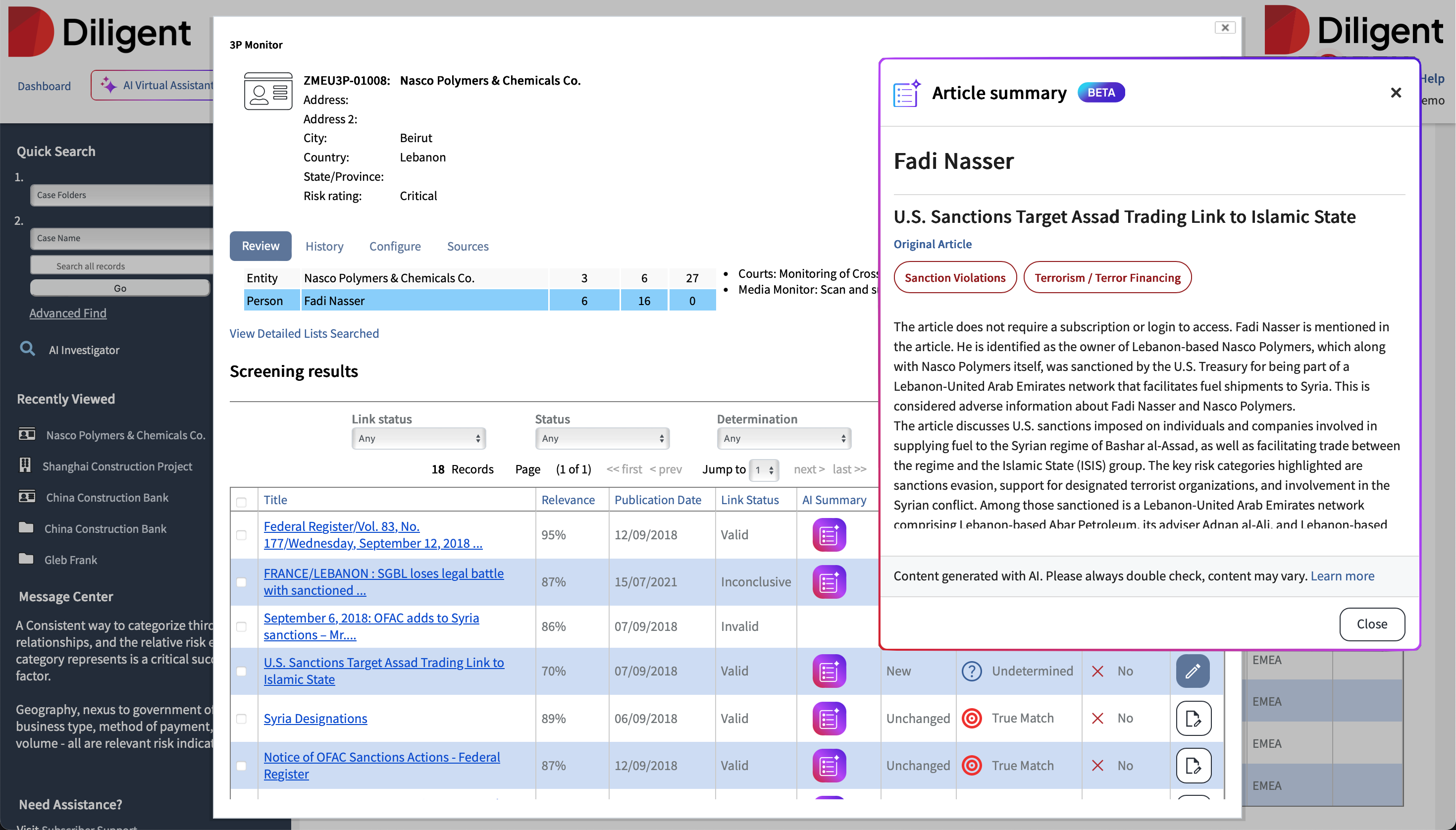
Effectively screen & monitor new partners
Save time and see deeper with our proprietary data- and AI-enabled business intelligence. Ensure transparency and mitigate hidden risks with Diligent's ultimate beneficial ownership search.
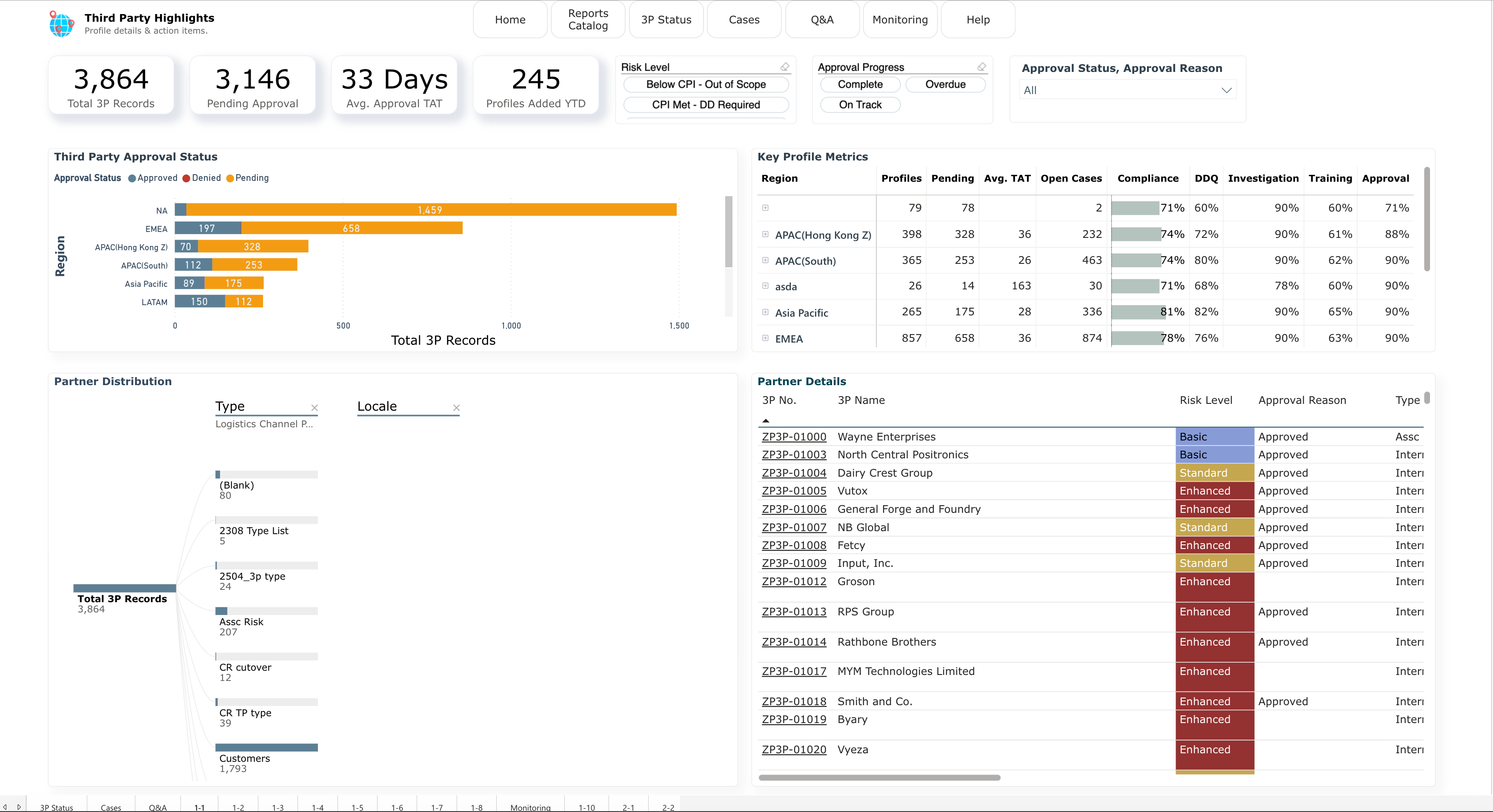
Streamline the third-party lifecycle
Drive efficiency with customizable workflows, automated screening, streamlined approvals, and compatibility with external systems.
Power your ABAC program with deep insight
Leverage out-of-the-box interactive analytics and reporting to track the health of your third-party due diligence, meaningful insights to respond proactively to trends instead of chasing them.
Make due diligence efficient and scalable
Apply the right level of screening based on actual risk. From automated database checks to comprehensive field investigations, match your due diligence depth to vendor risk levels for optimal resource allocation.
A simpler, smarter path to third-party assurance
Trusted by 200+ enterprise organizations worldwide
Everything you need to run a smarter risk program
Integrated regulatory & external risk data
Access sanctions, watchlists, PEPs, and adverse media—all curated and integrated to streamline third-party screening and monitoring.
No-code workflows & assessments
Built-in KRI/KPI metrics and benchmarking
More to love
Build trust into every third-party relationship
From onboarding to ongoing monitoring, discover how Diligent helps you create a defensible, scalable third-party risk program that adapts to changing threats — and stands up to scrutiny.
Don’t take it from us — take it from our 25,000+ customers
Frequently Asked Questions
Your question not answered here? Reach out to talk with us.
How does integration work with our existing systems?
We offer RESTful APIs and pre-built integrations with major ERP, procurement, and GRC platforms. Most enterprise implementations connect with existing workflows within 2-4 weeks using our integration toolkit.
What makes your AI-powered monitoring different?
Can we handle complex vendor ecosystems and fourth parties?
We have a complex global supply chain. Can this solution scale with us?
What level of due diligence services are available?
Take a smarter approach to third-party management
Strengthen your third-party relationships through transparency, accountability, and insight. Diligent empowers you to conduct rigorous due diligence, surface real-time risk signals, and monitor continuously — so you can safeguard your reputation while enabling the partnerships that drive your business forward.