Products
Solutions
Resources

Internal control weaknesses expose organizations to financial misstatements, fraud and regulatory penalties. For companies preparing for IPO or managing complex compliance requirements, unaddressed control deficiencies can derail transactions, trigger material weakness disclosures and erode stakeholder confidence.
According to Diligent's 2025 What Directors Think report, 61% of directors say a major cybersecurity incident would have "significant impact" on their company's strategy. Control weaknesses in IT systems, access management and change protocols often serve as entry points for such incidents.
This article explains what you need to know about identifying, classifying and remediating internal control weaknesses, including:
An internal control weakness is a gap or flaw in an organization's processes, policies or systems that increases the risk of errors, fraud or non-compliance. These weaknesses prevent the achievement of control objectives like accurate financial reporting, asset protection and regulatory compliance.
They can stem from:
Additionally, they range in severity from minor deficiencies to material weaknesses that pose significant risk of major financial misstatement. As such, identifying and remediating these weaknesses before they escalate is critical to maintaining stakeholder confidence and regulatory standing.
Understanding the classification hierarchy helps prioritize remediation efforts:
For pre-IPO companies, the distinction matters significantly. Material weaknesses identified during IPO can delay offerings, reduce valuations and shake investor confidence.
Internal control weaknesses can impact several system areas. Understanding where vulnerabilities typically emerge helps organizations focus assessment efforts effectively.
Hardware and software should have their own set of internal controls mapped to specific risks, including access management, change management and data availability. When organizations make infrastructure changes or introduce new technology, technical control weaknesses emerge if configuration or implementation fails.
Common technical weaknesses include inadequate user access provisioning, incomplete change management documentation and insufficient backup and recovery procedures.
Human error represents a fundamental limitation to even well-designed internal controls. Employees who don't follow or misunderstand control policies can unintentionally create operational weaknesses.
Building a culture of compliance addresses these weaknesses proactively, though effective incident response procedures remain essential when operational failures occur.
Administrative controls comprise the policies and procedures governing how employees engage with protected data. These controls include
Weaknesses in administrative controls often stem from outdated policies, unclear ownership assignments or insufficient training on control requirements.
Your security architecture determines how your systems identify and mitigate risk. Architectural weaknesses emerge when risk identification and resolution processes fail to function effectively.
This category includes segregation of duties gaps, inadequate monitoring capabilities and insufficient integration between systems that should share control data.
Beyond the categories where weaknesses occur, understanding how controls fail helps organizations build more effective assessment and remediation programs.
Design deficiencies exist when a control, even if operating perfectly, cannot prevent or detect material misstatements. According to the COSO framework, these represent fundamental gaps in control architecture.
Common design weaknesses include unclear control objectives that don't address actual risks, missing preventive controls, poor segregation of duties allowing single individuals to initiate and approve transactions, and controls that address only partial risk pathways.
Even well-designed controls can fail in practice. Operating effectiveness weaknesses occur when controls aren't performed consistently, documentation is incomplete or manual workarounds bypass established procedures.
Indicators include:
Information technology controls present particular challenges as systems grow more complex. IT weaknesses include inadequate access controls that allow unauthorized users into financial systems, change management gaps that permit untested modifications and weak data quality controls that allow errors to propagate through integrated systems.
Some weaknesses reflect organizational culture rather than specific control procedures. Entity-level weaknesses include tone at the top issues where leadership doesn't demonstrate commitment to controls, weak risk assessment processes, inadequate monitoring by those charged with governance and insufficient competence in financial reporting roles.
Having internal controls in place is vital. Even more important is identifying and getting ahead of weaknesses on an ongoing basis. These are the steps you can take to identify weaknesses in all areas of your system before they cause harm:
The foundation of weakness identification is thorough auditing across all control areas. Your internal audit function should examine existing hardware, software, policies, procedures and the people who interact with systems. The audit committee should receive regular updates on audit findings and control status.
Use audit findings to create a comprehensive catalog of all internal controls, including policies, procedures and responsible parties. This documentation serves as the foundation for ongoing assessment and provides evidence for auditors.
Effective documentation includes control objectives linked to specific risks, detailed control descriptions with ownership assignments and testing procedures with frequency requirements.
Risk assessment identifies where control weaknesses would have the greatest impact. Organizations should evaluate regulatory requirements across all jurisdictions, financial statement assertions requiring control support, fraud risk factors and emerging risks from technology changes or market conditions.
"There are mission-critical risks outside of internal audit's typical scope. You can't fill your audit plan with these risks, but you have to incorporate them into your planning," notes Keaton.
Human error introduces risk to well-designed controls. Training programs help employees understand control requirements and their role in maintaining effectiveness.
When people understand how their actions protect the organization, compliance becomes cultural rather than procedural.
Waiting for periodic audits to identify weaknesses allows problems to compound. Continuous monitoring detects issues as they occur, enabling prompt remediation before weaknesses escalate to material concerns.
Organizations should also establish compliance monitoring programs that integrate with control testing. Effective monitoring includes automated exception identification, real-time dashboards tracking control performance and trend analysis that spots control degradation early.
Identifying weaknesses is only valuable if organizations can effectively remediate them. The remediation process varies based on deficiency severity, but follows a consistent framework.
Not all control issues require the same response. Classification helps prioritize remediation resources. For example:
Before designing fixes, determine why the weakness exists. Common root causes include:
Addressing symptoms without fixing root causes leads to recurring deficiencies.
Develop specific remediation activities with clear ownership. For design deficiencies, this may involve creating new controls, redesigning existing ones or implementing technology to automate manual processes.
For operating effectiveness issues, remediation typically focuses on enhanced training, updated procedures or improved monitoring. Each corrective action should have a designated owner and realistic completion date.
After implementing changes, verify that controls now operate effectively. Testing should use the same rigor applied during initial deficiency identification.
For material weaknesses, SOX compliance requirements mandate disclosure of remediation status in quarterly filings until external auditors confirm the weakness is fully addressed.
Sustained remediation requires ongoing attention. Establish centralized tracking systems recording all deficiencies and their status, schedule regular progress reviews with executive and audit committee visibility and implement follow-up testing protocols to confirm controls remain effective over time.
Managing the identification and remediation challenges documented above requires more than spreadsheets and periodic reviews. When control testing, risk assessment and audit functions operate on disconnected platforms, the visibility gaps that allow weaknesses to escalate become inevitable.
That's why AI-powered internal controls management has become essential infrastructure for organizations building audit-ready control frameworks.
Diligent's Internal Controls enables organizations to save up to 80% of time on control testing through AI-powered control mapping that intelligently links controls to regulations.
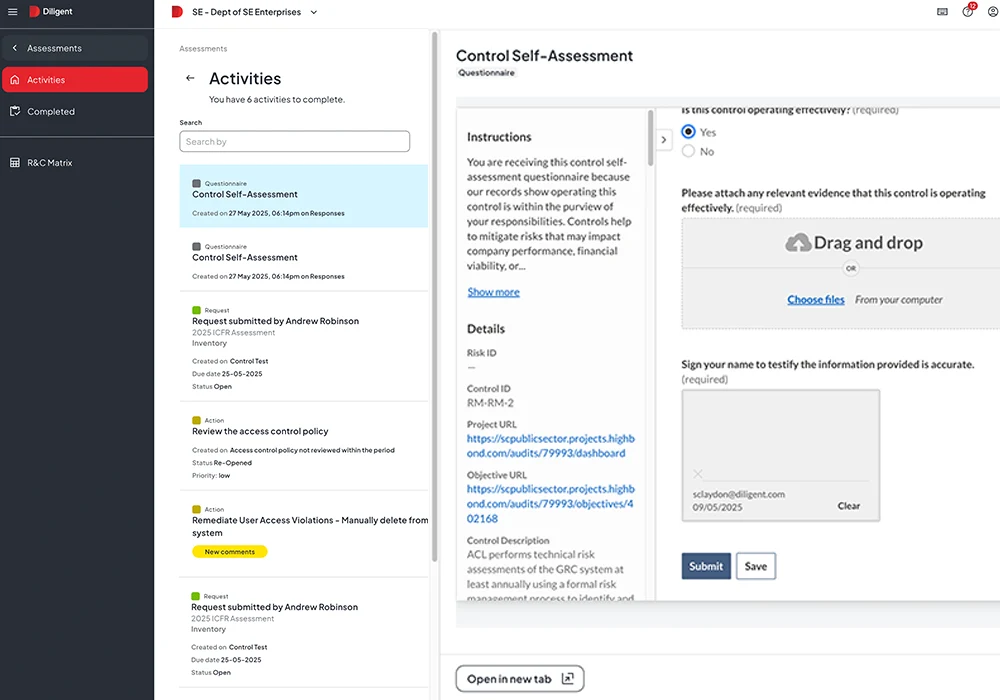
Real-time reporting provides audit-ready documentation, while automated workflows streamline testing, monitoring and evidence collection across the entire control lifecycle.
For audit teams requiring comprehensive data analysis, Diligent ACL Analytics moves beyond sample-based testing to examine 100% of transactions.
Natural language analytics capabilities allow non-technical auditors to run sophisticated tests, while automation robots deliver continuous assurance monitoring that identifies control degradation as it occurs rather than months later.
"We feel that with [Diligent], we've evolved as an audit team. It's not that we do more audits, but that we can provide better information," says Vincent Verlinde, National Risk and Assurance Manager at Daikin Australia.
The Diligent One Platform integrates these capabilities with enterprise risk oversight, audit coordination and board reporting. This unified approach to GRC provides the visibility that manual processes cannot achieve, connecting control weaknesses to broader risk patterns and ensuring audit committees receive timely, actionable intelligence.
Together, these capabilities create the integrated infrastructure that effective internal controls require. Control owners see their responsibilities clearly, compliance teams monitor in real time rather than quarterly and audit functions provide continuous assurance rather than point-in-time assessments.
Ready to strengthen your internal controls with AI-powered detection and remediation? Schedule a demo to see how Diligent connects control testing, risk management and audit functions on a unified platform.
An internal control weakness is any condition where a control's design or operation fails to prevent or detect errors. A material weakness, on the other hand, is the most severe classification, indicating a reasonable possibility that a material misstatement could occur without being caught.
Common causes include inadequate segregation of duties, insufficient management review processes, weak IT general controls around financial systems, lack of competent personnel in key positions and poor tone at the top.
Many weaknesses also stem from rapid organizational growth that outpaces control infrastructure.
Testing frequency depends on control criticality and risk level. High-risk controls typically require annual testing at minimum, with many organizations moving toward quarterly or continuous testing.
Timelines vary based on severity and root cause. Simple operating effectiveness issues may resolve within one quarter. Design deficiencies requiring system changes typically take 6-18 months.
Material weaknesses often require multiple quarters to fully remediate, with ongoing disclosure until complete.
Key metrics include percentage of controls tested on schedule, number and severity of deficiencies identified, average remediation cycle time and audit findings trends. Organizations should also track coverage metrics showing what percentage of high-risk areas receive continuous versus periodic monitoring.
Request a demo to discover how Diligent's AI-powered platform can help identify weaknesses faster and build audit-ready control frameworks.