Products
Solutions
Resources

For general counsel at large public companies, enterprise data risk management has become a governance obligation that sits squarely on the board's agenda rather than being buried in IT's quarterly update. Regulators expect documented oversight structures. Institutional investors scrutinize proxy disclosures for evidence of active board engagement.
Independent directors ask pointed questions about risk appetite, incident-escalation protocols, and cross-functional coordination. The gap between having a cybersecurity program and demonstrating board-level governance of data risk is precisely where fiduciary exposure accumulates.
If you already understand why data risk matters, what you need is a credible framework for building the oversight infrastructure your board, your auditors and the SEC expect to see, before a regulatory examination or material incident forces the conversation under pressure. This article provides that framework and covers:
Why SEC disclosure rules and SOX requirements have made data risk a board governance obligation
The regulatory and fiduciary landscape has fundamentally shifted. Data risk is no longer an operational concern that boards can delegate without structured oversight: It is a governance obligation with specific disclosure requirements and documented liability exposure.
The SEC's cybersecurity disclosure rules created two interconnected mandates. Form 8-K Item 1.05 requires disclosure of material cybersecurity incidents within four business days of a materiality determination. Regulation S-K Item 106 requires annual disclosure in the 10-K of the board's specific oversight structure for cybersecurity risks, the processes by which the board is informed and management's role and expertise.
These are affirmative disclosure obligations that create accountability for the quality of board oversight, not just its existence. The standard these rules establish is specificity, because generic boilerplate about cybersecurity governance cannot satisfy requirements designed to give investors comparable, decision-useful information.
The SEC reinforced these expectations through enforcement. In October 2024, the Commission charged four companies — Unisys Corporation, Avaya Holdings, Check Point Software Technologies and Mimecast Limited — not for failing to disclose incidents but for making materially misleading characterizations of cybersecurity risks. The enforcement actions established that the standard is accuracy and completeness, with disclosure language itself becoming a focus alongside incident timing.
Sarbanes-Oxley compounds this exposure. Section 302 certifications and Section 404 internal control assessments now necessarily encompass cybersecurity controls affecting financial data integrity, thereby making audit committees statutorily responsible for overseeing the data systems that underpin financial reporting.
A material weakness in cybersecurity controls affecting financial systems can trigger an adverse internal control conclusion requiring disclosure in the 10-K. KPMG analysis shows how the SEC rule intersects with existing audit committee oversight expectations.
Directors face potential personal liability for failing to implement reporting systems that monitor mission-critical risks or for sustained inattention to red flags. Cybersecurity has reached that threshold for most public companies.
"Data risk" means different things to the legal team, the CISO, the procurement function and the board. A mature oversight framework must define and address all four dimensions, as material exposure most often accumulates at their intersections.

Here's how enterprise data risk manifests across your organization:
Most enterprise risk frameworks treat these four dimensions in functional silos. That fragmentation is where material exposure accumulates, because incidents rarely confine themselves to a single dimension. A vendor breach simultaneously triggers compliance obligations, operational disruptions, reputational consequences and board disclosure requirements.
Satisfying board and regulatory expectations requires six interconnected components. Each one addresses a specific governance gap that regulators, auditors and institutional investors actively scrutinize.
Define what counts as data risk across the organization so every business unit, committee and reporting function operates from a shared vocabulary. The COSO risk framework provides a widely recognized starting point. The taxonomy should include standardized severity scales, both qualitative and quantitative, so risk appetite discussions at the board level are grounded in consistent definitions rather than subjective assessments.
Boards need to understand data risk in business terms, not technical ones. This requires structured business impact analysis that connects data assets to the processes, revenue streams and regulatory obligations they support.
When a director asks "what happens if this system goes down for 48 hours?" the answer should quantify revenue impact, regulatory exposure, contractual liability and recovery time, not describe server configurations.
Point-in-time risk assessments, even quarterly ones, are insufficient for a threat environment that changes daily. Mature programs establish continuous monitoring with defined key risk indicators (KRIs) that provide real-time visibility into risk posture changes.
According to What Directors Think 2026 by Diligent Institute and Corporate Board Member (a Fall 2025 survey of 200+ U.S. public company directors), 28% of directors cite a large-scale cybersecurity breach as a top risk to their organizations.
So what? Treat cyber/data KRIs as "between-meeting" signals, not quarterly discussion points: define a small set of KRIs tied to business impact (e.g., ransomware dwell time, privileged access exceptions, critical vendor control failures), set board-approved thresholds, and require automated alerts to the CISO, GC and committee chairs when those thresholds are breached.
According to the NACD audit report, 64% of S&P 500 audit committees now oversee cybersecurity risks, and the organizations leading this practice have moved beyond periodic assessments to continuous monitoring that surfaces emerging risks between scheduled board meetings. To apply this insight, audit committees should mandate automated KRI tracking that triggers immediate alerts when risk thresholds are breached, rather than waiting for the next quarterly update.
Data risk findings must feed directly into the internal controls framework, not sit in a separate report that never reaches the audit committee. SOX 404 requires management assessment and auditor attestation of internal controls over financial reporting, and cybersecurity controls affecting financial data integrity are squarely within scope. Disconnected risk and control processes create the exact gaps that external auditors flag and regulators investigate.
Risk committees need structured, recurring visibility with consistent metrics and trend lines, not ad hoc updates triggered by incidents. Establish a three-tiered reporting cadence: quarterly comprehensive risk committee meetings with substantive agendas, monthly executive summaries to the board chair and committee chairs and immediate escalation protocols for material incidents requiring board notification within hours.
Board-level dashboards should be concise: six to eight pages maximum, with key metrics including risk heat maps, KRI trends, and exposure-versus-appetite thresholds.
In a regulatory examination, shareholder derivative action or SEC inquiry, the audit trail is the defense. Board meeting minutes must document the specific questions directors asked, the challenges they raised, and the management follow-ups they assigned. "Received report" in meeting minutes signals passive oversight. "Board challenged management's assessment of vendor risk concentration, directed follow-up assessment within 60 days" signals active governance.
Board reporting must prioritize transparency and comprehension, focusing on the organization's most valuable assets and highest risks, using visual formats understandable by non-technical board members, including risk heat maps, progress tracking, and residual risk indicators that enable informed challenge rather than passive acceptance.
Documentation requirements extend beyond meeting minutes to include materiality determinations, risk appetite approvals and escalation decisions.
The oversight components outlined above require infrastructure that connects risk, audit, compliance and legal workflows, without creating another silo.
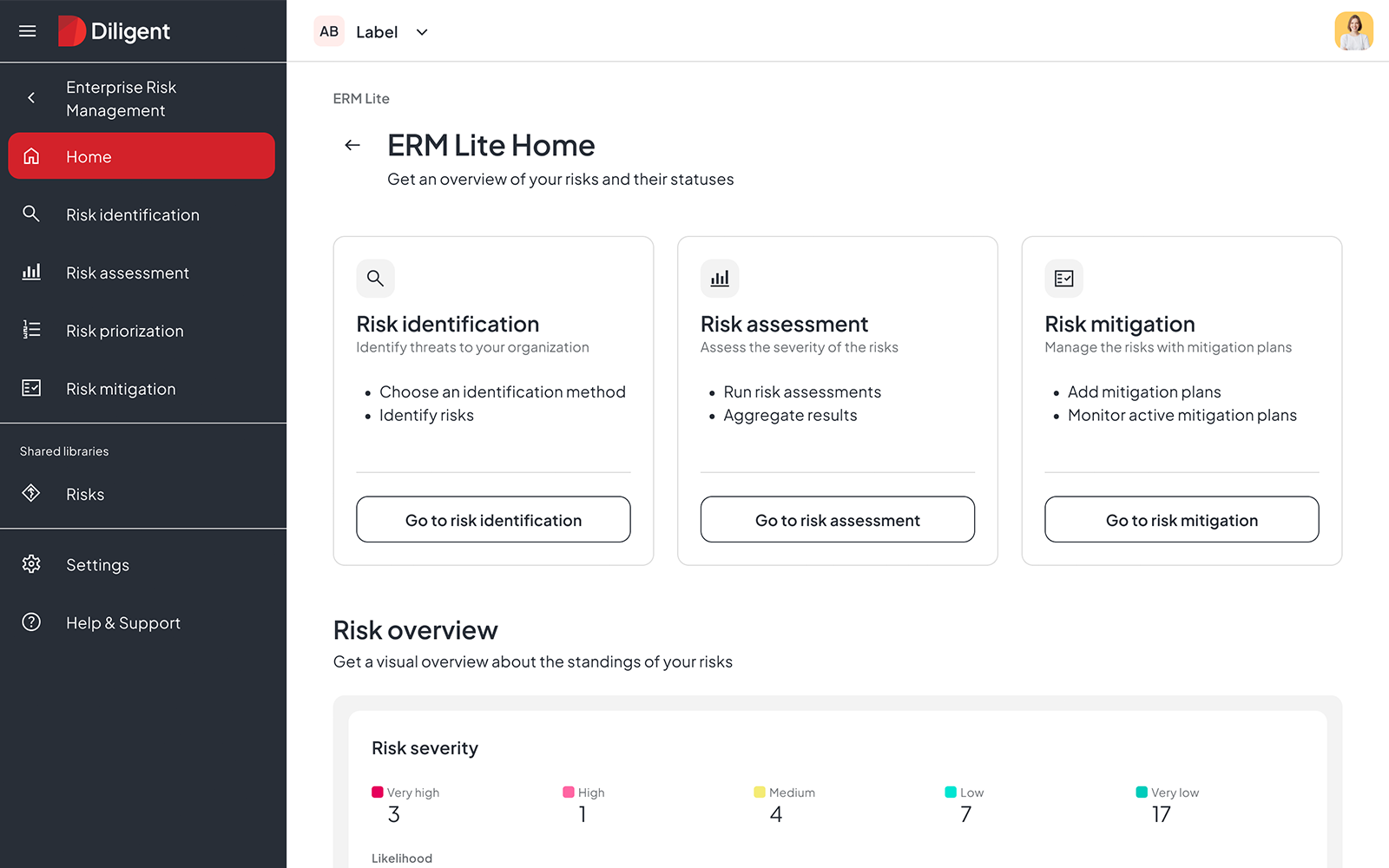
Together, these capabilities support a consistent reporting cadence, credible oversight documentation and faster escalation decisions — the mechanics that regulators and sophisticated boards expect to see.
The framework outlined here, risk taxonomy, business impact mapping, continuous monitoring, internal controls integration, board reporting cadence and rigorous documentation, represents more than a compliance obligation. When implemented deliberately, it becomes institutional infrastructure that strengthens every governance decision the board makes.
General counsel who build this infrastructure proactively create a fundamentally different dynamic than those who assemble it under the pressure of a regulatory examination or material incident. Boards equipped with structured oversight processes, consistent metrics and documented deliberation govern data risk with confidence rather than react to it defensively.
The organizations that treat governance quality as a strategic differentiator, not merely a regulatory burden, earn credibility with institutional investors and proxy advisory firms and regulators whose scrutiny will only intensify. In an environment where data risk touches every dimension of enterprise value, the quality of board oversight is itself a competitive asset.
See how Diligent enables enterprise data risk governance that earns institutional investor confidence. Schedule a demo
The most common model assigns cybersecurity and data risk oversight to the audit committee, which aligns with existing SOX responsibilities for financial reporting integrity. Some organizations establish dedicated risk committees or technology committees, depending on the complexity of their data risk profile.
Regulation S-K Item 106 requires annual disclosure of the board's oversight structure for cybersecurity risks, including which committee is responsible, how the board is informed and management's role and expertise. Form 8-K Item 1.05 requires disclosure of material cybersecurity incidents within four business days. The 2024 enforcement actions against Unisys, Avaya, Check Point and Mimecast demonstrate that the SEC scrutinizes accuracy and completeness, not just existence.
Best practice establishes a three-tiered cadence: quarterly comprehensive risk committee meetings, monthly executive summaries to the board chair and relevant committee chairs and immediate notification protocols for material incidents.
Data risk findings affecting financial systems are important for SOX 404 assessments, but SOX 404 and related SEC/PCAOB guidance do not explicitly require that such findings must flow directly into the ICFR framework. Access control gaps, data integrity issues and system availability risks should be classified as control deficiencies, assigned remediation owners with documented timelines and tracked through resolution.
Courts evaluating director oversight under Caremark examine whether the board implemented reasonable information and reporting systems and whether directors responded appropriately to red flags. Meeting minutes should document the specific questions directors asked, the challenges raised, and the follow-up actions assigned, not simply that reports were "received and filed."
General counsel who build structured, documented oversight infrastructure position their boards to govern data risk with confidence rather than react to it under pressure. Schedule a demo to see how Diligent supports institutional-grade risk governance.